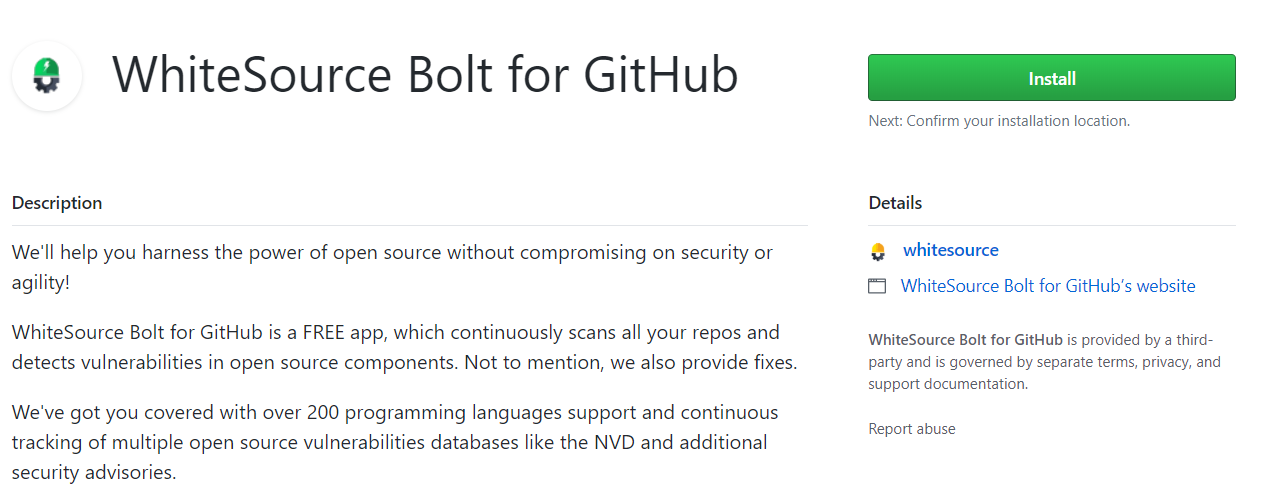
WhiteSource Bolt for GitHub is a GitHub app, scanning your GitHub.com repositories at no cost (GitHub Enterprise Server is not supported). The app can be installed from the GitHub marketplace- https://github.com/marketplace/whitesource-bolt.
It is an integrated product within GitHub that detects all open source components in your repository and alerts on vulnerabilities for these components.
WhiteSource Bolt for GitHub detects all open source components in your software, without ever scanning your code.
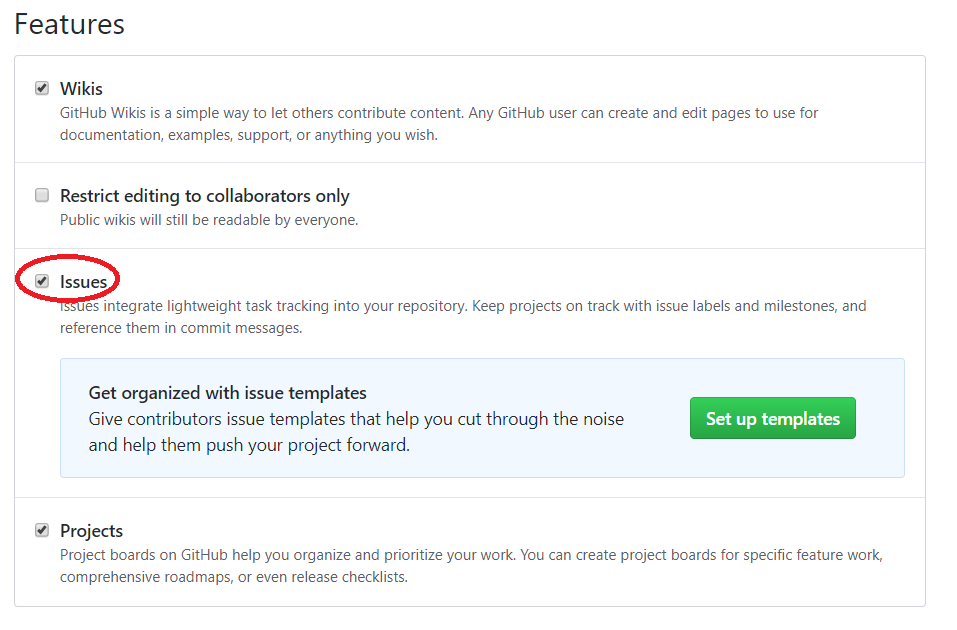
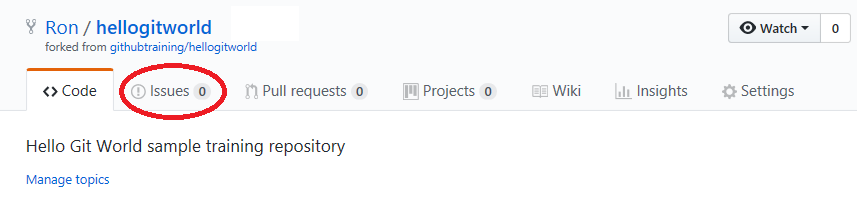
It provides you with issues on vulnerable open source components and generates comprehensive up-to-date reports on the GitHub 'Issues' tab of the scanned repository.
For more information or questions on WhiteSource Bolt for GitHub, please reach out directly to boltgithub@whitesourcesoftware.com.
GitHub repositories requiring access to artifacts in local registries are not supported. |
Bolt for GitHub does not scan archived GitHub repositories, since their 'read only' status blocks various actions that are required during the scan. |
Installation is done via the following link. Click on the 'Install' button on the page that opens.
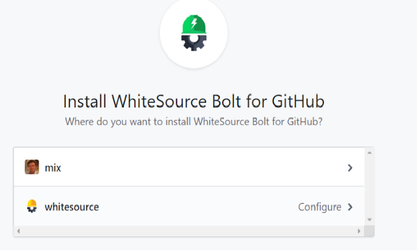
If you have more than one GitHub account then you should initially confirm your installation location by selecting the GitHub account(s) for which you would like to install the WhiteSource Bolt for GitHub app. Click on the 'Configure' link for the relevant account.
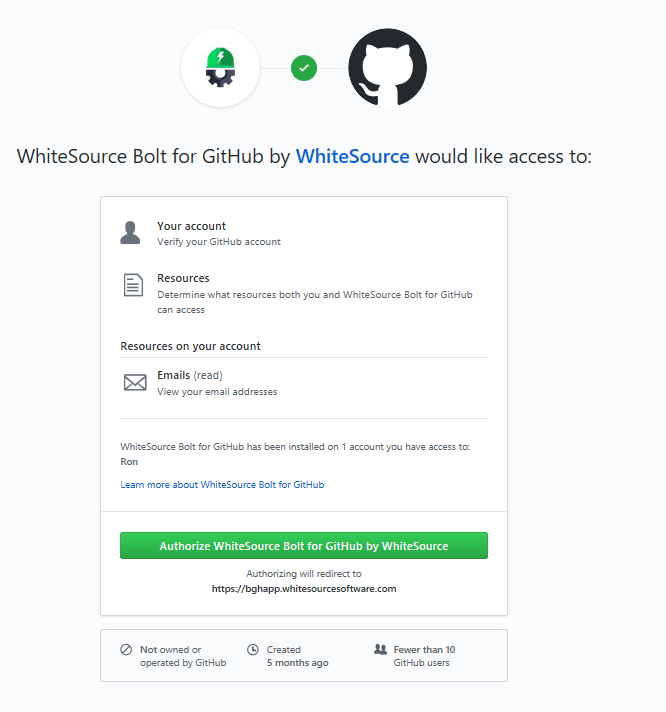
The following screen is displayed for the selected account or in cases that you have only one GitHub account:
Select one of the following options:
The app does not scan archived GitHub repositories, since their 'read only' status blocks various actions that are required during the scan. |
Read the permissions that must be provided for the WhiteSource Bolt for GitHub app to work, and then click on the 'Authorize WhiteSource Bolt for GitHub by WhiteSource' button.
After the installation, the following registration form appears with your email address filled in:
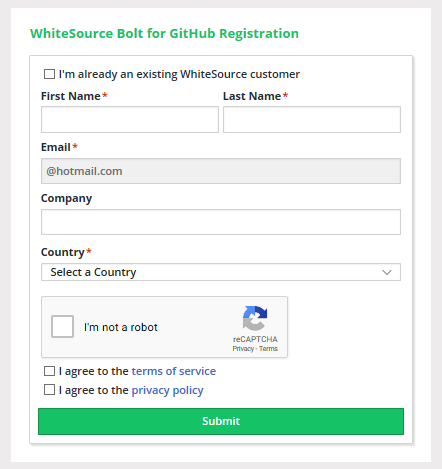
Fill in all the required fields, select the required checkboxes, and then click the 'Submit' button.
If the form page accidentally closes before you clicked on the 'Submit' button then you can use the link in the registration email message that was sent to you in order to complete the registration process. Use this link only in cases where the form screen has been closed before the 'Submit' button was clicked. This feature is only available when your GitHub email address is not marked as Private. |
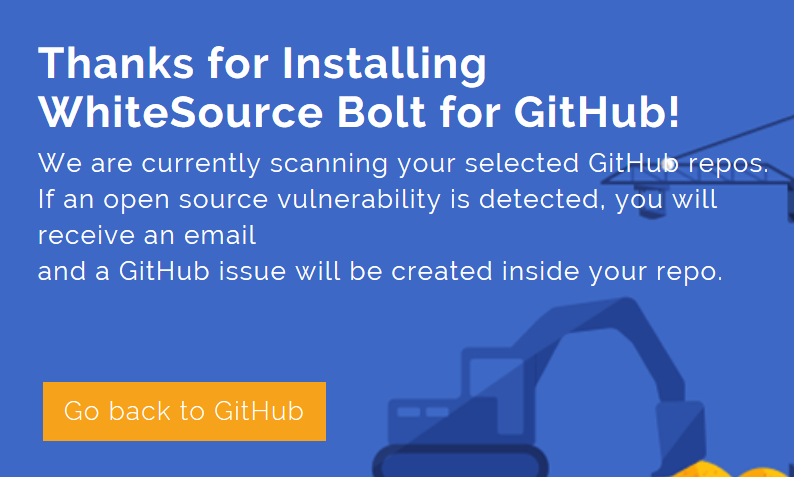
You will be forwarded to the Bolt for GitHub 'Thanks for Installing' page. Click on the 'Go back to GitHub' button to return to your GitHub account page.
After selecting your repositories, an onboarding pull request is created. This pull request contains a WhiteSource configuration file (.whitesource) that can be customized before merging the pull request. Once the pull request is merged, a WhiteSource scan will be initiated.
At this stage, Bolt has started scanning your selected repositories. If a vulnerability is detected, then you will receive an email, and an issue will be created in your GitHub's project 'Issues' tab. The scanning process may take a number of minutes.
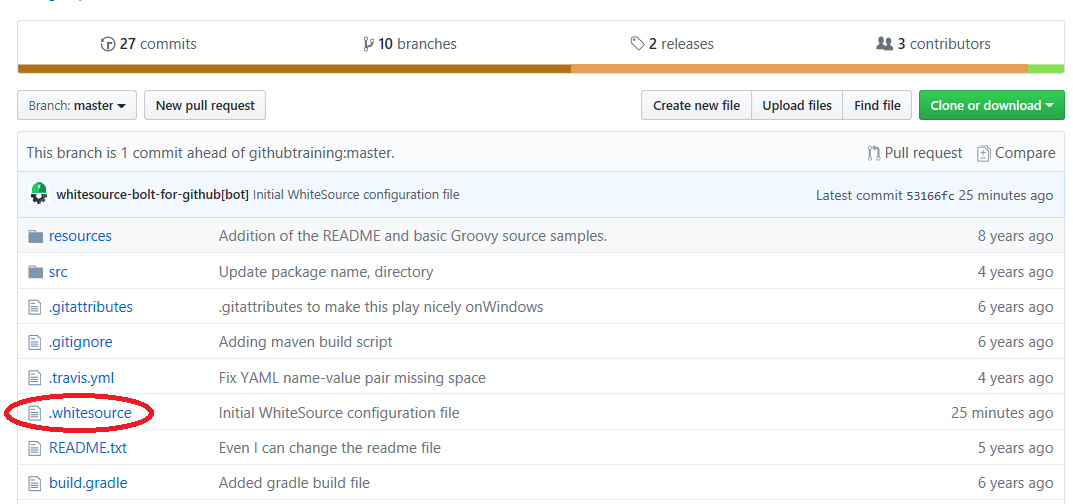
A WhiteSource configuration file ('.whitesource') is added to each repository that is enabled for a scan. It provides configurable parameters for the WhiteSource scan. The '.whitesource' file is only added in the default branch of the repository (unless modified, it is the master branch). Any configuration change that is done to this file must be in the default branch of the repository.
{
"checkRunSettings": {
"vulnerableCheckRunConclusionLevel": "failure"
},
"issueSettings": {
"minSeverityLevel": "LOW"
}
} |
| Parameter | Type | Description | Required | Default |
|---|---|---|---|---|
| vulnerable.check.run.conclusion.level | String | The app utilizes the GitHub Checks API that provides checks in commits and pull requests on any repository branch. This parameter defines the conclusion status for when a WhiteSource Security Check is completed. When the parameter is set to 'success', the conclusion status of a WhiteSource Security Check will always be 'Success', even if the check fails. This way, any repository member is able to merge a pull request, even if a WhiteSource Security Check found security vulnerabilities. When the parameter is set to 'failure' (default), the conclusion status of a WhiteSource Security Check will be 'Failure' in cases where WhiteSource Security Check found security vulnerabilities or an error occurred during the scan. When this configuration is defined, and a branch protection rule has been added, a policy for approving a pull request is enforced. In this setting, only the administrator of the repository can approve the merging of a pull request that contains one or more checks with a 'Failure' status. See also Initiating a Merge Policy. | No | failure |
| Parameter | Type | Description | Required | Default |
|---|---|---|---|---|
| minSeverityLevel | String | Enables users to decide whether to open a new GitHub Issue only if a certain Severity Level is available. Available values for "minSeverityLevel" needs to be:
| No | LOW |
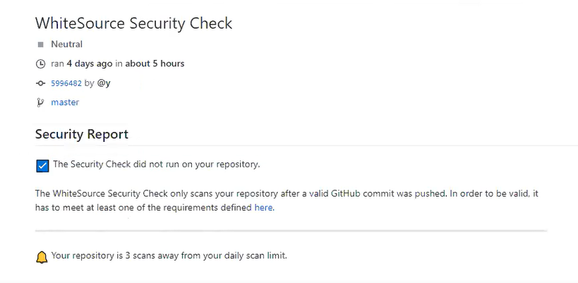
New users are entitled to scan each repository up to five times a day. Existing WhiteSource customers have the scan limitations that are set in their account agreement with WhiteSource.
A scan is initiated via a valid GitHub 'push' command. A valid 'push' command meets at least one of the following requirements:
Any metafile with one of the following extensions:
Each time a valid GitHub 'push' command is made for a repository, WhiteSource initiates a scan;
|
WhiteSource supports pull requests for the shared repository model (see also this GitHub article). In this case, topic branches are created in the same repository by maintainers to be later be in pull requests against the production branch (usually the master branch).
The administrator of the repository then decides whether to merge the pull requests. See also about-collaborative-development-models.
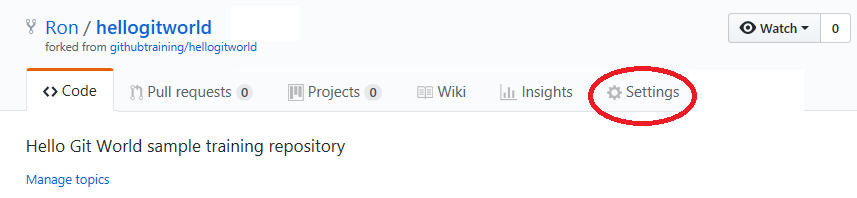
Results are viewed on the 'Issues' tab of the repository on GitHub and via email notifications.
If you are making 'push' commands via the Web browser then click the 'Refresh' button of the Web browser in order to view the issues that were found.
It may take a number of minutes for the issues to be scanned and displayed after a valid 'push' command is initiated. |
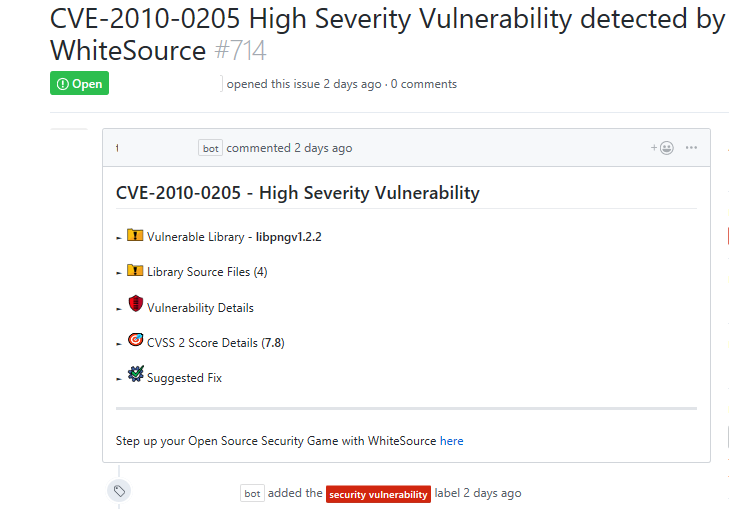
The 'Issues' tab displays all the issues that WhiteSource Bolt for GitHub detected with the red 'security vulnerability' label. This proprietary label indicates a security vulnerability was detected by WhiteSource.
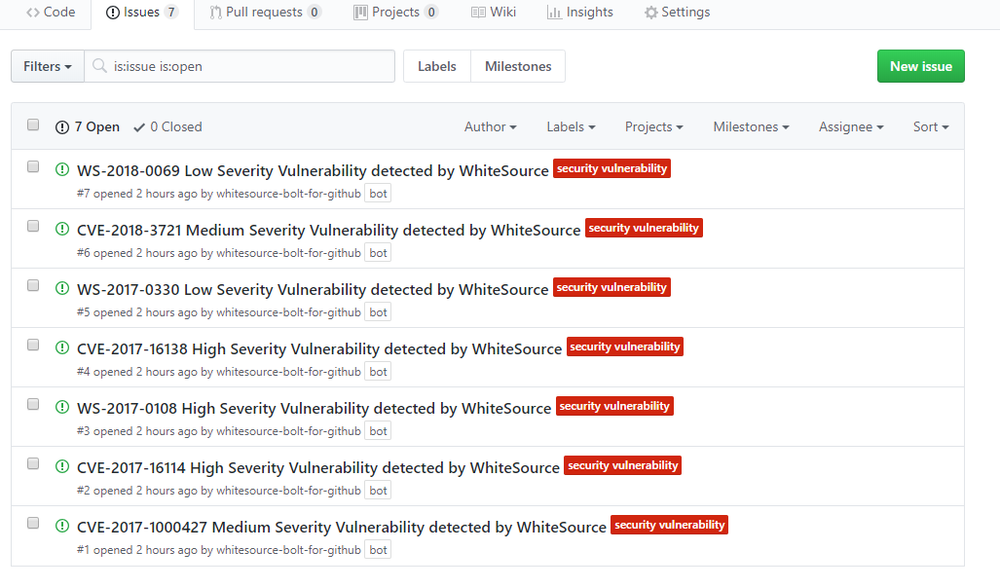
As part of your workflow, you have the option to add relevant label(s) to specific issues, and close issues that were resolved.
All manually closed issues are not resent or reopened as open issues during the next scan unless their label and/or name has been manually changed or changed via an API. |
Clicking on a specific issue displays its details:
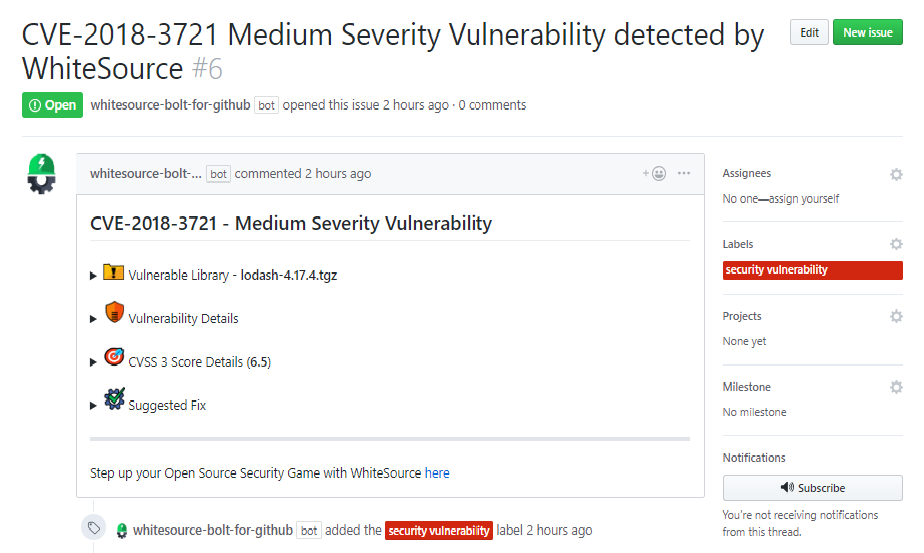
Click on an item's list bullet ( ) to view more information on it.
) to view more information on it.
The display changes according to the type of library:
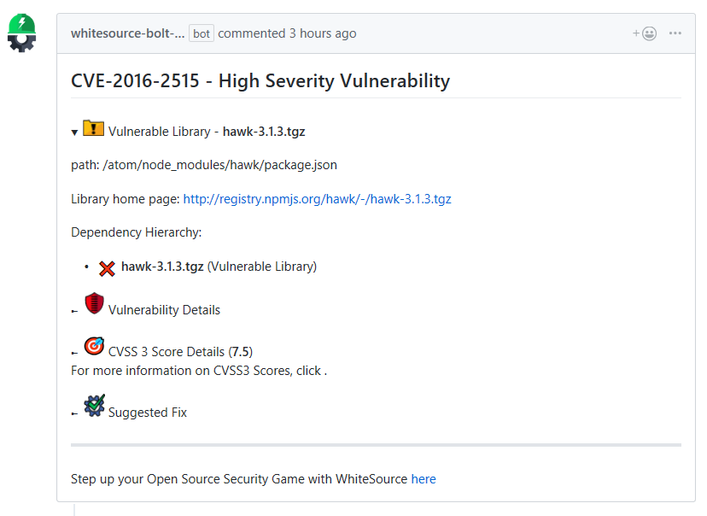
Vulnerable library: Includes the path of the library. If the path is of a transitive dependency library then only the path information of the root library is relevant to you.
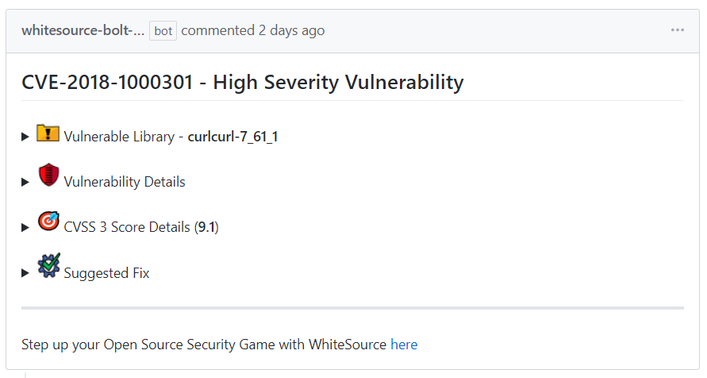
WhiteSource supports displaying multiple libraries for the same CVE when such a case occurs. |
As part of your workflow, you have the option to use various GitHub tasks for a specific issue such as the tasks in the 'Assignees', 'Labels', 'Projects', 'Milestone', and 'Notification' sections. You can also add and edit comments for a specific issue.
After the scan is made, a separate email message is sent on each issue as shown in this sample screenshot of a typical email message on a vulnerability that was found:
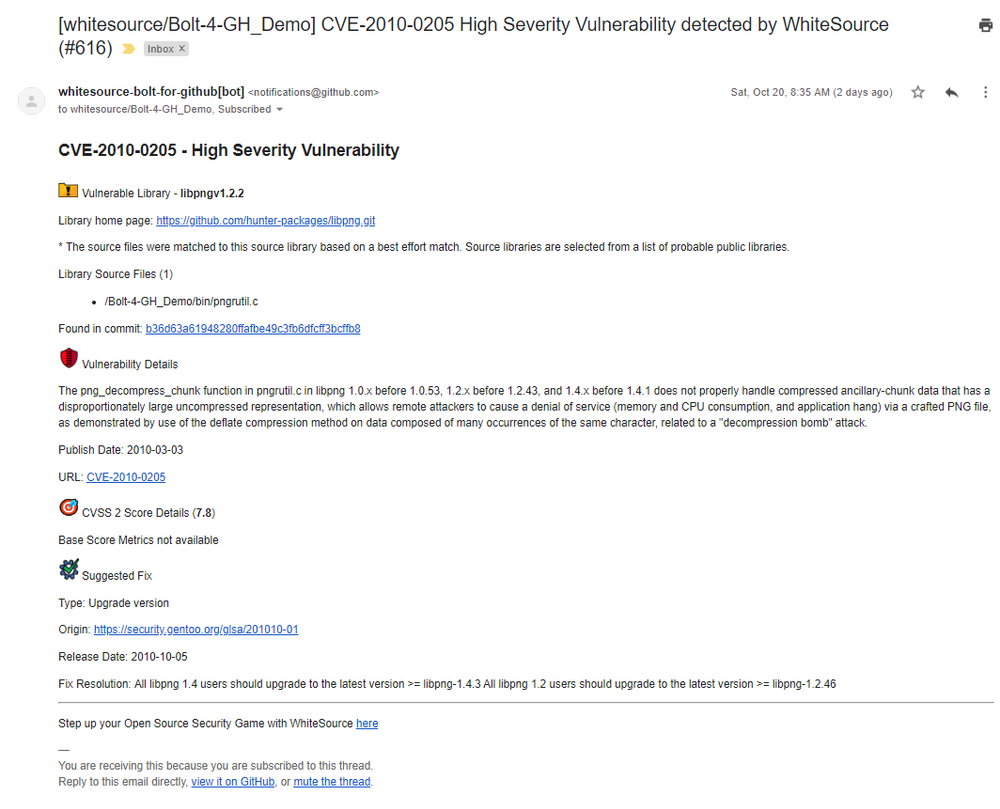
The information in the email message is identical to the displayed information on the 'Issues' tab.
A merge policy utilizes the app's integration with GitHub Checks API. It enables the repository's administrator to approve the merging of a pull request with 'Failed' commit statuses to a target branch in the repository.
For more information on Checks API, see the related GitHub Checks API introduction page.
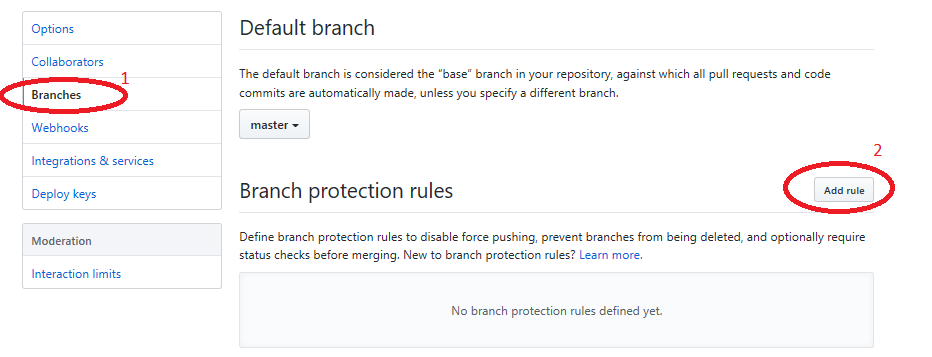
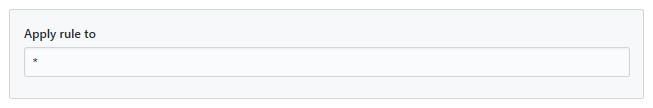
In order to enable a merge policy based on the conclusion of a WhiteSource Security Check, you must initially add the following GitHub rule for branch protection:
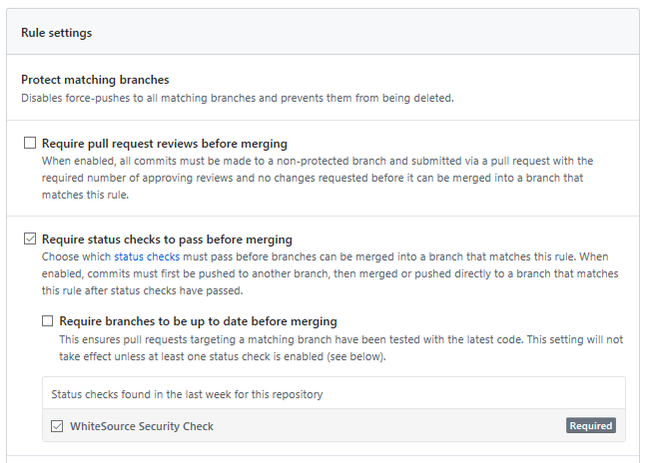
Checks API indicators are displayed for each head commit on the 'Commits' section of the 'Code' tab. Clicking on a specific indicator opens a pop-up window that displays further details on the status:
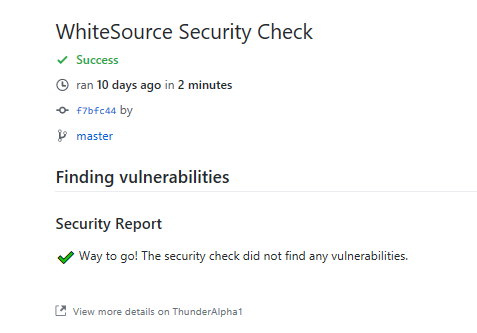
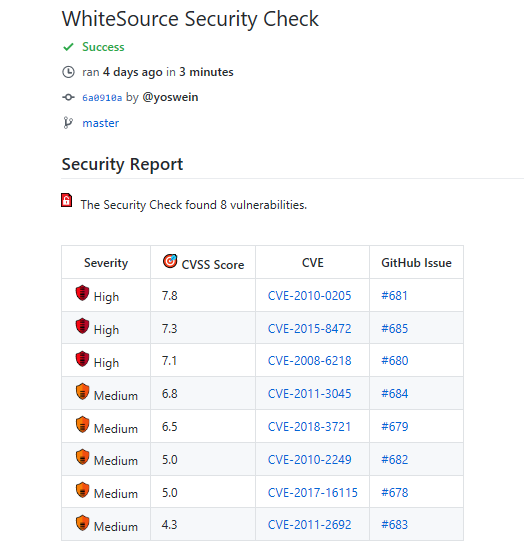
Clicking on the 'Details' link in the pop up window displays the WhiteSource Security Check page for the selected head commit. The page includes the conclusion status of the head commit along with a Security Report:
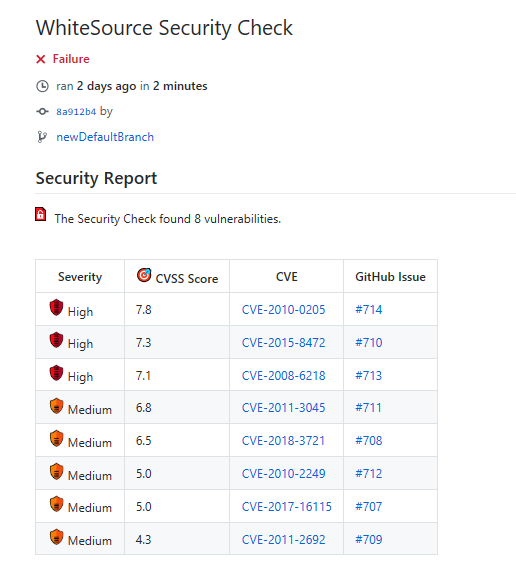
The security report displays all the vulnerabilities that were found in descending order according to the severity and CVSS score. The following information is displayed for each vulnerability:
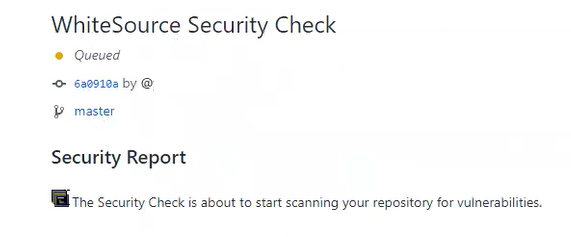
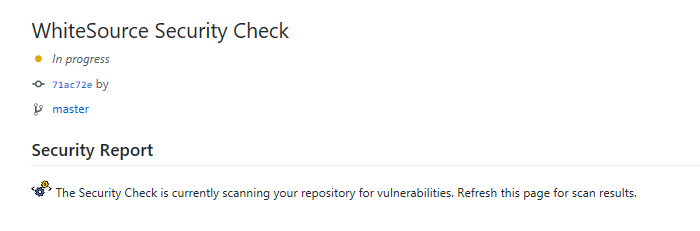
The following Checks API status indicators are available as a feedback on the head commits:
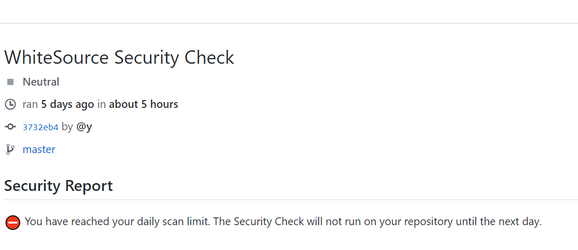
Neutral: conclusion occurs when the repository has reached its daily limit of scans, and the next scan will be on the next day or when the push command was not valid.
The following is a sample of a 'Queued' status, which indicates that the security check is about to start scanning the head commit's vulnerabilities.
The following is a sample of an 'In-Progress' status, which indicates that the security check is currently scanning the head commit.
The status can be displayed in two scenarios:
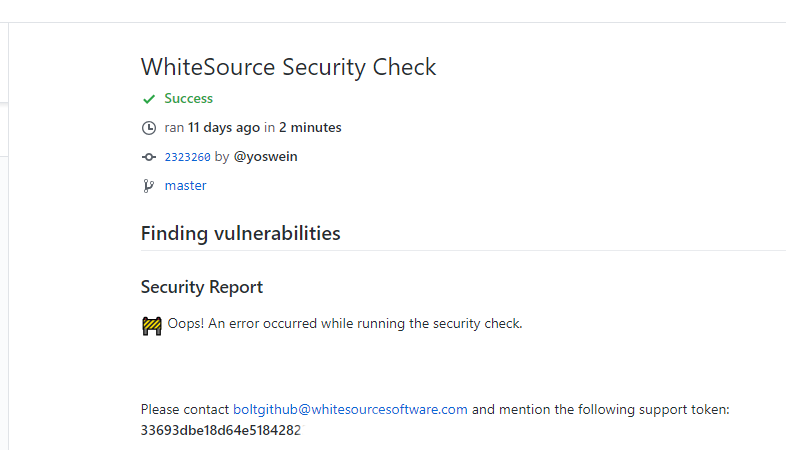
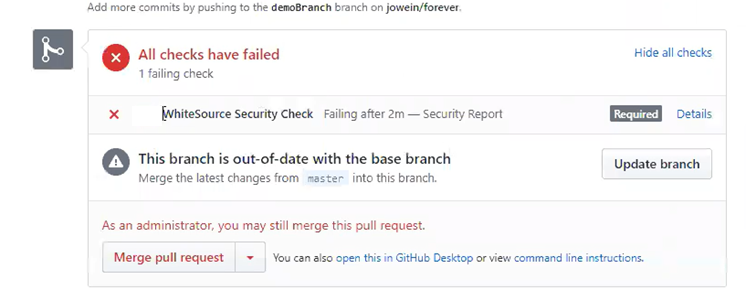
When the parameter 'vulnerable.check.run.conclusion.level' is set to ''failure', all head commits that fail the scan due to the security check or due to an error that occurred during the scan display a 'failure' status. The following screenshot displays a 'failure' indicator for a head commit that includes high severity vulnerabilities, since the parameter 'vulnerable.check.run.conclusion.level' is set to 'failure'. In this case, only the administrator of the repository can approve merging a pull request that includes this head commit to another branch in the repository, and therefore, it will not be automatically merged.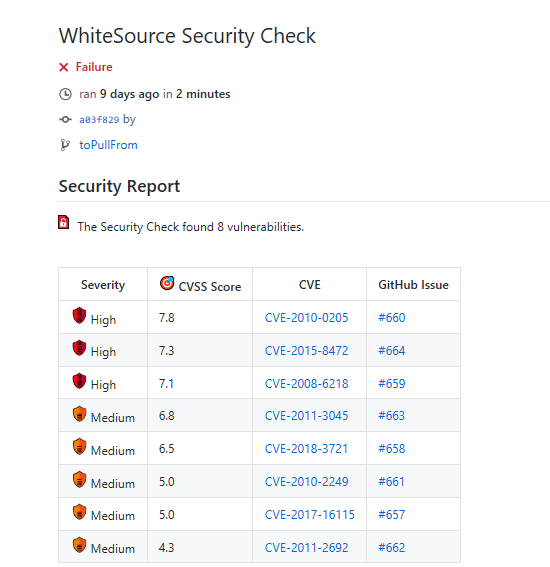
The following screenshot is a sample of the display in a pull request page when a 'failure' policy is enforced and one or more of its head commits have a 'failure' status. Only the administrator of the repository can approve the merging of a pull request with a 'failure' status:
A neutral conclusion occurs in one of the following scenarios:
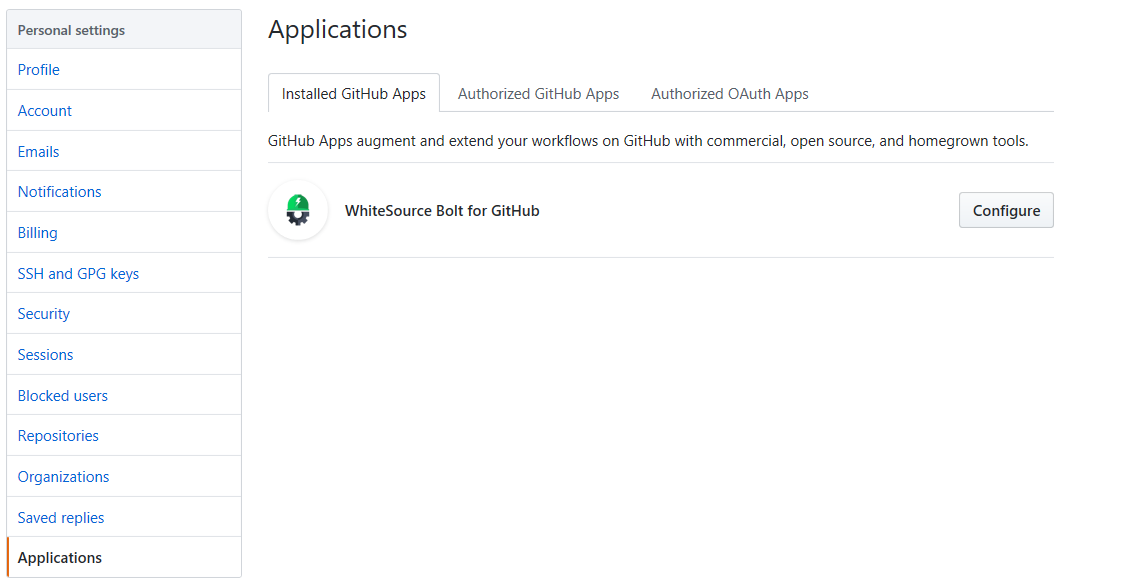
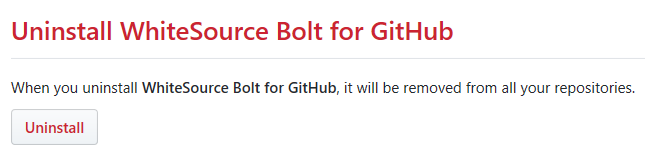
You can easily uninstall this app by doing the following: