This is a controlled WhiteSource integration release. For more information, please contact support@whitesourcesoftware.com. |
This integration only supports Bitbucket Server and Bitbucket Data Center instances. It does not currently support Bitbucket Cloud instances. |
WhiteSource for Bitbucket Server is a Bitbucket Server app, scanning your repositories, as part of your WhiteSource account.
It is an integrated product within Bitbucket Server that shows a high-level security overview in the Bitbucket repository, detects all open source components and displays all vulnerabilities for these components.
It generates comprehensive up-to-date reports on the Bitbucket Server ‘WhiteSource integration’ tab of the scanned repository. In addition, you will be able to view the scanned repositories in the WhiteSource portal.
WhiteSource for Bitbucket Server is part of WhiteSource for Developers and includes continuous automated dependency updates with WhiteSource Remediate, using fix Pull Requests.
The following requirements must be accommodated before installing the WhiteSource server software.
This build environment can be the same one as the deployment environment on which the WhiteSource Docker image is deployed. It requires the following:
docker –version |
The image is installed on the target environment. This environment requires the following:
CPU: Dual Core, 2Ghz or higher (Intel or AMD)
RAM: 16GB
Storage: 16 GB
A user with admin privileges: If the operating system is Windows, then you must have administrative privileges. If the operating system is Linux, then you must have root privileges.
docker –version |
The access to the app can be checked by issuing an HTTP GET request using a web browser or a utility (e.g., cURL, wget): It is recommended to verify that the returned status is 200 (OK). |
Download the ‘tar.gz’ file (‘agent-4-bitbucket-<version>.tar.gz’) for Linux or 'zip' file Windows (‘agent-4-bitbucket-<version>.zip’)
In Windows, extract ‘agent-4-bitbucket-<version>.zip’ to an empty folder. In Linux, extract ‘agent-4-bitbucket-<version>.tar.gz’ to an empty folder.
The extraction creates the following items:
See here for more information on which package managers are part of the scanner image as well as how to add additional package managers.
There are two ways to install the WhiteSource App in Bitbucket Server - by installing the app via the Atlassian marketplace for Bitbucket, or by uploading the JAR file directly from the extracted WhiteSource for Bitbucket folder.
Navigate to the Administration page (<your/bitbucket-server/url>:<port>/admin) and then click Find new apps under the ADD-ONS menu.
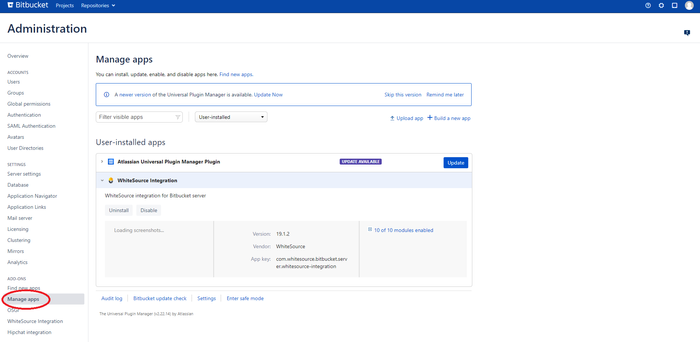
Navigate to the Administration page (<your/bitbucket-server/url>:<port>/admin) and then click Manage apps under the ADD-ONS menu.
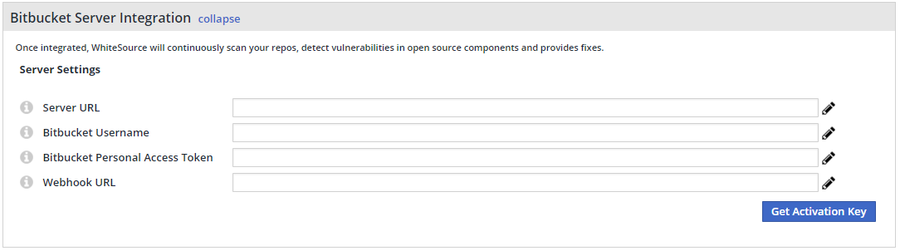
The displayed fields are the following:
This editor enables you to configure the deployment file according to your specific configuration requirements.
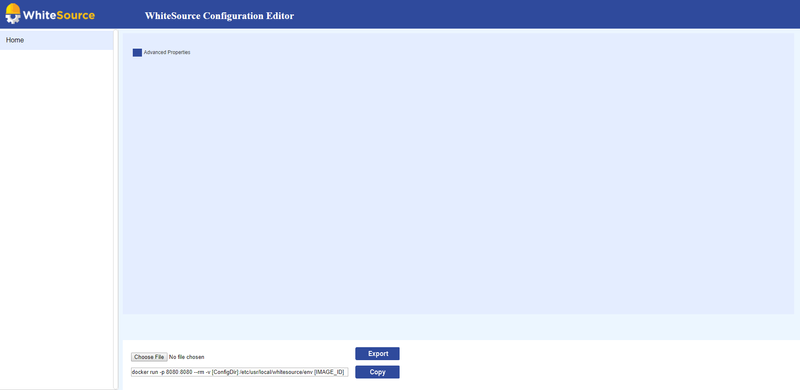
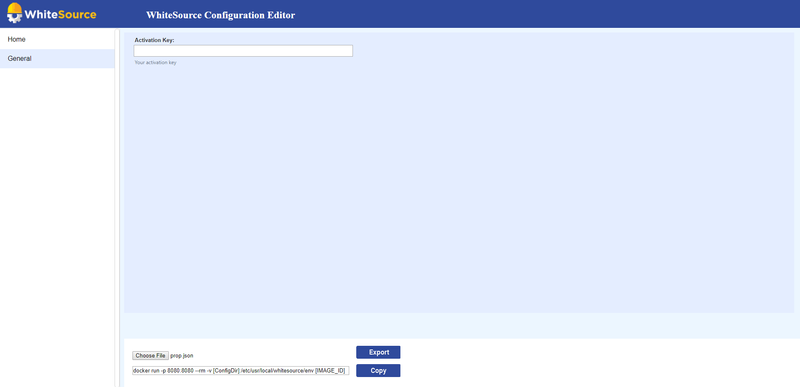
Please copy the Activation key that was generated in WhiteSource application and paste it to 'Activation Key' property in the editor.
| Section | Label | Name | Type | Mandatory | Description | Sample Value |
|---|---|---|---|---|---|---|
| General | Activation Key | bolt.op.activation.key | String | yes | Your generated activation key in the WhiteSource application | |
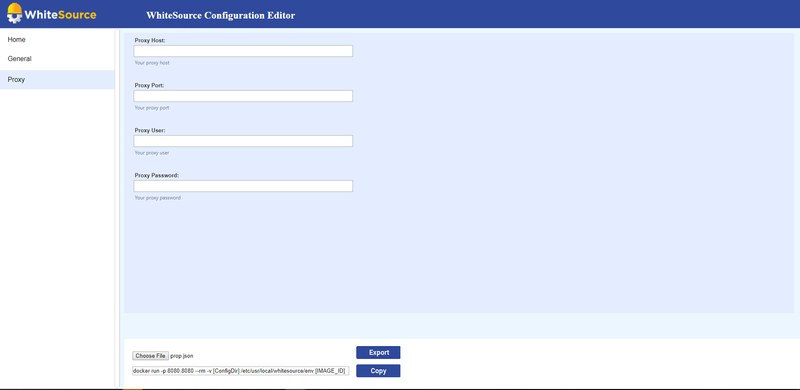
| Proxy | HTTP Proxy Host | proxy.host | Host Address | no | HTTP proxy host. Leave blank to disable. Default value: Empty | |
| Proxy | HTTP Proxy Host | proxy.port | Integer | no | HTTP proxy port. Leave blank to disable. Default value: Empty | |
| Proxy | Proxy User | proxy.user | String | no | Proxy Username (if applicable) | user |
| Proxy | Proxy Password | proxy.password | String | no | Proxy Password (if applicable) | abc123 |
| Advanced | Controller URL | controller.url | String | no | The ability to modify the App container URL in case its default name (wss-bb-app) was modified. Default value: http://wss-bb-app:5678 | http://wss-bb-app:5678 |
| Issues | Should Create Issues | bolt4scm.create.issues | Boolean | no | The ability to globally enable/disable Issues creation across all of your organization's repositories. Default value: true (NOTE: Supported from version 20.5.1.3 only) | |
| Issues | Should Create Build Status | bolt4scm.create.check.runs | Boolean | no | The ability to globally enable/disable build statuses across all of your organization's repositories. Default value: true (NOTE: Supported from version 20.5.1.3 only) |
You can export the JSON file at any time, even if you did not finish editing it in order to save your configurations and to enable assigning the configuration of a specific section to the appropriate professional in your organization (e.g., datasource section may be assigned to the DBA of your organization). |
See also the ‘Configuring Deployment Settings’ section in this document.
Optional step: If you want to pull the images from another machine and run them as a container, push them to your Docker registry.
There are three different ways of building the Docker images.
A total of 3 images will be built: wss-bb-app, wss-scanner, and wss-remediate. |
Run the build.bat or build.sh executable script file (Windows/Linux).
Both files are located in the root of the extracted agent-4-bitbucket-<version>.zip or agent-4-bitbucket-<version>.tar.gz files.
For Windows:
Run build.bat file which is located in the main folder where you extracted the agent-4-bitbucket zip file.
In order to ensure that the build succeeded, run the command docker images and check if wss-bb-app and wss-scanner and wss-remediate images were created.
For Linux:
Run build.sh file which is located in the main folder where you extracted the agent-4-bitbucket tar.gz file.
In order to ensure that the build succeeded, run the command docker images and check if wss-bb-app and wss-scanner and wss-remediate images were created.
To run the steps of the build file manually, run the following commands directly:
NOTE: If you have already run the build file, skip these steps and continue to Target machine: Running the Containers step.
docker build -t wss-bb-app:<version> wss-bb-app/docker docker build -t wss-scanner:<version> wss-scanner/docker docker build -t wss-remediate:<version> wss-remediate/docker # For example: docker build -t wss-bb-app:19.9.1.1 wss-bb-app/docker docker build -t wss-scanner:19.9.1.1 wss-scanner/docker docker build -t wss-remediate:19.8.1 wss-remediate/docker |
If you are using a private Docker Registry, run the following commands to push the images into your registry:
docker push <registry>/wss-bb-app:<version> docker push <registry>/wss-scanner:<version> docker push <registry>/wss-remediate:<version> # For example: docker push my-registry/wss-bb-app:19.9.1.1 docker push my-registry/wss-scanner:19.9.1.1 docker push my-registry/wss-remediate:19.8.1 |
After executing the commands, you should be able to view the images in your registry.
On the target environment, create a directory (e.g., ‘<path/to/config/dir>’) and add to it the configuration properties JSON file (prop.json) that you previously edited and exported using the Configuration Editor.
Then, you will need to create a network bridge and run the following Docker containers by using Docker or Kubernetes.
Create a network bridge (this will create a private network between the different containers, since all containers need to run within the same network):
docker network create -d bridge my_bridge |
Run the ‘wss-remediate’ server container:
docker run --name remediate-server --network my_bridge -e LOG_LEVEL=debug -p 8080:8080 -v <path/to/config/directory>/prop.json:/etc/usr/local/whitesource/conf/prop.json -v /tmp:/tmp wss-remediate:<version> # For example: docker run --name remediate-server --network my_bridge -e LOG_LEVEL=debug -p 8080:8080 -v c:/tmp/bb/prop.json:/etc/usr/local/whitesource/conf/prop.json -v /tmp:/tmp wss-remediate:19.5.1 |
If port 8080 is not available, you can use a different port by modifying only the second port in the 'docker run' command. For example: docker run --name remediate-server --network my_bridge -e LOG_LEVEL=debug -p 8082:8080 -v c:/tmp/bb/prop.json:/etc/usr/local/whitesource/conf/prop.json -v /tmp:/tmp wss-remediate:19.5.1 |
Run the 'wss-bb-app' app container:
docker run --name wss-bb-app --network my_bridge -p 9494:9494 -p 5678:5678 -v <path/to/config/directory>:/etc/usr/local/whitesource/conf wss-bb-app:<version> # For example: docker run --name wss-bb-app --network my_bridge -p 9494:9494 -p 5678:5678 -v c:/tmp/bb/:/etc/usr/local/whitesource/conf/ wss-bb-app:19.5.1.1 |
Run the ‘wss-scanner’ scanner container:
docker run --name wss-scanner-bb --restart=always --network my_bridge -p 9393:9393 -v <path/to/config/directory>:/etc/usr/local/whitesource/conf/ wss-scanner:<version> # For example: docker run --name wss-scanner-bb --restart=always --network my_bridge -p 9393:9393 -v c:/tmp/bb/:/etc/usr/local/whitesource/conf/ wss-scanner:19.5.1.1 |
The wss-deployment folder consists of the following structure:
Copy the helm folder from wss-deployment to your target environment. Inside the helm/configs folder, add the configuration properties JSON file (prop.json) that you previously edited and exported using the Configuration Editor.
This file contains information about the chart.
NOTE: Do not edit this file.
This file represents the WhiteSource integration image names and versions.
wsscanner:
image: {image}
version: {version}
wsscontroller:
image: {image}
version: {version}
wssremediate:
image: {image}
version: {version}
For each image declaration (wssscanner, wsscontroller, wssremediate), replace {image} and {version} with the actual built image name and version. NOTE: For wsscontroller, use the name and version of the wss-bb-app image.
An optional parameter, imagePullSecrets, can be added to this file in case Docker repository authentication is required.
In the helm folder, create a new folder named configs, and add to it the configuration properties JSON file (prop.json) that you previously edited and exported using the Configuration Editor.
This is a configuration file pointing to the configs/prop.json file.
NOTE: Do not edit this file.
This is a configuration file containing all the parameters for deploying the integration.
NOTE: In this file, there are 3 dashes ("- - - ") that separate the services Do not remove them.
In order for the webhook URL to be accessible publicly by the integration, a load balancer service must be added to the file. An example of such a service is provided below:
apiVersion: v1
kind: Service
metadata:
name: lb1
namespace: acme
annotations:
external-dns.alpha.kubernetes.io/hostname: helm.acme.io
service.beta.kubernetes.io/aws-load-balancer-backend-protocol: http
service.beta.kubernetes.io/aws-load-balancer-ssl-ports: "443"
service.beta.kubernetes.io/aws-load-balancer-ssl-negotiation-policy: "ELBSecurityPolicy-TLS-1-2-2017-01"
service.beta.kubernetes.io/aws-load-balancer-ssl-cert: arn:aws:acm:us-east-7:834027593108:certificate/4720e07a-a231-4fd5-9c4a-12ab1450567d
spec:
type: LoadBalancer
ports:
- port: 443
name: https
targetPort: 5678
selector:
app: wss-controller
WhiteSource Remediate provides continuous automated dependency updates, saving time and reducing your security risks. To read more and configure automated Pull Requests, see WhiteSource Remediate
A WhiteSource scan is initiated via a valid Bitbucket push command. A valid push command meets at least one of the following requirements:
One of the commits in the push command added/removed a source file(s) that has an extension supported by WhiteSource.
Refer to the WhiteSource Languages page in order to find out whether or not a specific language and its extensions are supported.
One of the commits in the push command includes an addition/modification of the package manager dependency file(s).
Refer to the list of supported dependency files to find out whether your dependency files are supported.
NOTE: a push command may consist of multiple commits.
Results can be viewed in the following places:
See here for more information.
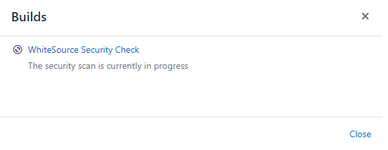
In the Commits tab you can view the status and results of each scan. Click a specific build icon in order to view the Builds page.
The following build status indicators are available as feedback on the head commits:
The following is a sample of a In Progress status, which indicates that the security check is currently scanning the head commit.
When no vulnerabilities are found and no errors occurred during the scan, WhiteSource will display the following status check, and a security report indicating that no vulnerabilities were detected:
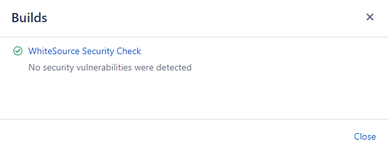
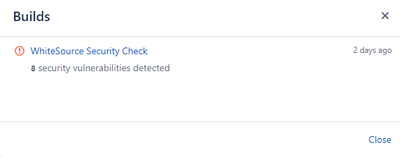
Click on the ‘WhiteSource Security Check’ link to view the security report on all vulnerabilities that were found for the specific commit’s scan. It includes the following columns:
In the Commits tab you can view the status and results of each scan. Click a specific build icon in order to view the Builds page.
The following build status indicators are available as feedback on the head commits:
See here for more information.
See here for more information.
A WhiteSource configuration file (.whitesource) is a JSON file added to each repository that is enabled for a scan. It provides configurable parameters for the WhiteSource scan.
{
"scanSettings": {
"configMode": "AUTO",
"configExternalURL": "",
"projectToken": "",
"baseBranches": []
},
"buildSettings": {
"displayMode": "diff",
"failBuilds": true
},
"issueSettings": {
"minSeverityLevel": "LOW"
}
} |
| Parameter | Type | Description | Required | Default | ||
|---|---|---|---|---|---|---|
| settingsInheritedFrom | String | When the global configuration is enabled, this parameter will specify the location of the whitesource-config repository from which it will inherit its configuration. It must contain the Bitbucket user name, repository name and branch (optional) of the repo-config.json file location. The default branch is 'master', but can be modified according to the location of the repo-config.json file in the whitesource-config repo. NOTE: You can override specific parameters that are relevant only in the specific repository by adding these after this parameter. Examples: Using only values defined in the global configuration:
Using values defined in the global configuration and overriding the scan settings parameters:
| No | N/A |
Parameter | Type | Description | Required | Default |
|---|---|---|---|---|
| configMode | String | The configuration mode to be used for each scan. There are three options:
| No | Auto |
| configExternalURL | String | The URL of the external configuration file (you can choose any filename). The configuration file content should be in the same format as the Unified Agent configuration file. The following protocols are supported: 'ftp://', 'http://', 'https://'. For example: 'https://mydomain.com/whitesource-settings/wss-unified-agent.config' | No | Empty |
| projectToken | String | Adds the ability to map a Bitbucket repository to a WhiteSource project. The parameter used needs to be the WhiteSource project token. NOTE: Not supported in the Global Configuration. | No | Empty |
| baseBranches | Array | Adds the ability to specify one or more base branches for which scanning results will be sent to a new WhiteSource project. Example usage: ["master", “integration"] This will set both master and integration branches as base branches. Note the following:
NOTE: This parameter is available only from version 20.7.1. | No | Empty In this case, the base branch only consists of the default branch. |
| enableLicenseViolations | Boolean | When enabled, a new WhiteSource License Check will be generated for each valid push. NOTES:
| No | false |
Parameter | Type | Description | Required | Default | |
|---|---|---|---|---|---|
| displayMode | String | How to display WhiteSource security information for a scan performed on a non-base branch:
| No | diff | |
| failBuilds | Boolean | The app provides checks in commits and pull requests on any repository branch. This parameter defines the conclusion status for when a WhiteSource Security Check is completed. When the parameter is set to false, the conclusion status of a WhiteSource Security Check will always be 'Success', even if the check fails. This way, any repository member is able to merge a pull request, even if a WhiteSource Security Check found security vulnerabilities. When the parameter is set to true (default), the conclusion status of a WhiteSource Security Check will be 'Failure' in cases where WhiteSource Security Check found security vulnerabilities or an error occurred during the scan. When this configuration is defined, a policy for approving a pull request is enforced. In this setting, only the administrator of the repository can approve the merging of a pull request that contains one or more checks with a 'Failure' status. | No | true | |
| failLicenseBuilds | Boolean | The app provides checks in commits and pull requests on any repository branch. This parameter defines the conclusion status for when a WhiteSource License Check is completed. When the parameter is set to false, the conclusion status of a WhiteSource License Check will always be 'Success', even if the check fails. This way, any repository member is able to merge a pull request, even if a WhiteSource License Check found license policy violations. When the parameter is set to true (default), the conclusion status of a WhiteSource License Check will be 'Failure' in cases where WhiteSource License Check found license policy violations or an error occurred during the scan. When this configuration is defined, a policy for approving a pull request is enforced. In this setting, only the administrator of the repository can approve the merging of a pull request that contains one or more checks with a 'Failure' status. | No | true | |
| showWsInfo | Boolean | Whether to show additional WhiteSource information such as the project token inside the WhiteSource Build Status (after the scan token). WhiteSource information is only displayed if the commit originated from a base branch. The following hidden JSON object will also be added inside the Build Status when this parameter is enabled:
| No | false |
| Parameter | Type | Description | Required | Default |
|---|---|---|---|---|
| minSeverityLevel | String | Enables users to decide whether to open a new Issue only if a certain severity level is available on a detected vulnerability. Available values for minSeverityLevel:
NOTE: The WhiteSource Security Check summary is also affected by this parameter. | No | LOW |
| displayLicenseViolations | Boolean | Whether to generate an Issue for every detected license policy violation. NOTE: This parameter is relevant only if enableLicenseViolations (scanSettings) is set to true. | No | true (only if enableLicenseViolations (scanSettings) is set to true) |
| Parameter | Type | Description | Required | Default |
|---|---|---|---|---|
| enableRenovate | Boolean | When enabled, Remediate will raise automated Pull Requests for outdated dependencies in addition to Pull Requests remediating vulnerable dependencies. Remediate will then perform all the functionality and support all the configuration options available in WhiteSource Renovate. See Renovate configuration options for all configuration options. Refer here for parameter usage. | No | false |
| transitiveRemediation | Boolean | Whether to enable transitive remediation for NPM repos. When npm v6 (npm v7 is not currently supported) is used with a package-lock.json file, and vulnerabilities are found within transitive dependencies in the file, then in most cases Remediate is able to successfully remediate the vulnerability. Sometimes it may not be possible to successfully remediate because a parent dependency does not yet have a new release that allows the necessary fixed-in version of the transitive dependency. | No | false |
NOTE: Supported from version 20.5.1.3 only.
You can provide a custom .whitesource configuration file as part of the wss-bb-app container, in order to apply it globally to all of your organization's repositories. Doing so will apply the file to all onboarding pull requests for newly-selected repos. Repos which were already selected and activated before this change will not be affected by this global configuration. Only newly onboarded repos will be affected.
To apply this global change, do as follows:
Stop currently-running Docker containers from the previous version:
docker stop <wss-bb-app> <wss-scanner> <remediate-server> |
Remove the Docker containers from the previous version:
docker rm <wss-bb-app> <wss-scanner> <remediate-server> |
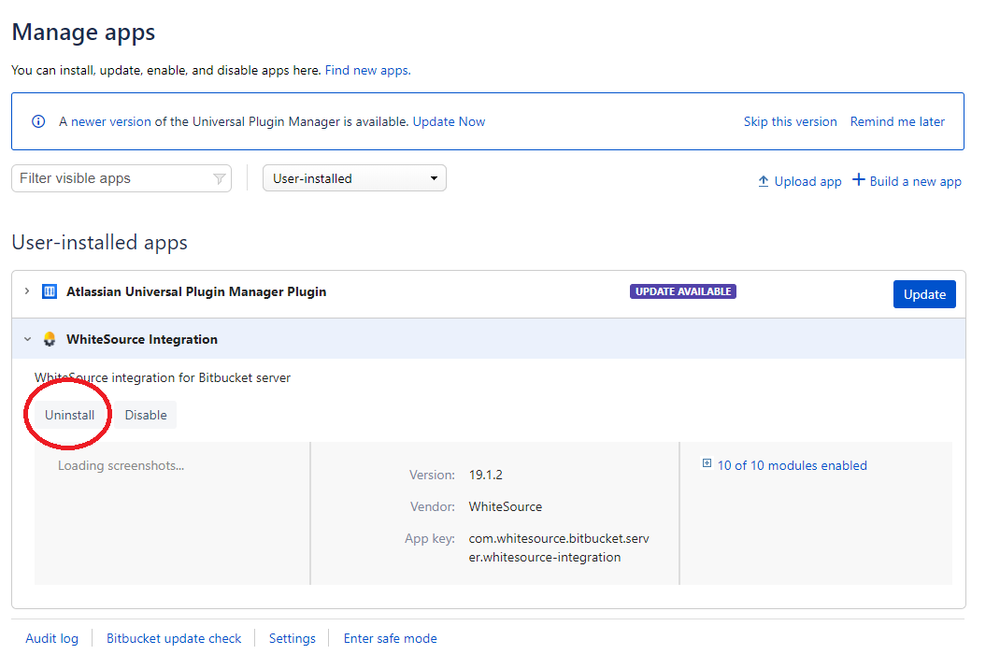
You can easily uninstall this add-on by doing the following: