...
| Table of Contents |
|---|
Overview
WhiteSource Mend Remediate automatically opens fix Pull Requests for vulnerable open-source components, upgrading them to the lowest non-vulnerable version. WhiteSource Mend Remediate is part of WhiteSource Mend Developer Integrations and integrated with WhiteSource Mend for GitHub.com, WhiteSource Mend for GitHub Enterprise, WhiteSource Mend for Bitbucket Server, and WhiteSource Mend for GitLab. Providing additional capabilities for project dependency health, Remediate is integrated with WhiteSource Mend Renovate (see below for details). Renovate enables you to save time and reduce risk by automating dependency updates in software projects.
WhiteSource Mend Remediate provides the following capabilities:
...
NOTE: A fix Pull Request is only generated for security vulnerabilities discovered on your repo's base branches, including transitive dependencies in npm.
Supported Package Managers
Package Manager | Language | Extra Details |
|---|---|---|
Maven | Java | N/A |
Gradle | Java | N/A |
Go Modules | Golang | Remediate will update both the |
npm/Yarn | JavaScript | WhiteSource Mend Remediate always updates both the package file (e.g. package.json) as well as any lock file (e.g. yarn.lock) in the same commit/fix Pull Request. |
NuGet | .NET | Only SDK-style
To convert your .NET Framework .csproj into an SDK-style project, follow this guide. |
pip | Python | N/A |
pipenv | Python | N/A |
poetry | Python | N/A |
setuptools | Python | N/A |
Composer | PHP | N/A |
NOTE: In WhiteSource Mend for GitLab, mirrored repositories are not supported.
...
Mend Workflow Rules
WhiteSource Mend Remediate is configured via custom Workflow Rules. To set up Workflow Rules for all or a selected list of WhiteSource Mend Products/Projects, do as follows:
From the WhiteSource Mend web application, click the Integrate tab.
Expand the WhiteSource Mend for Developers option.
From within the relevant repo integration settings, click Manage Workflow Rules. The Workflow Rules page is displayed.
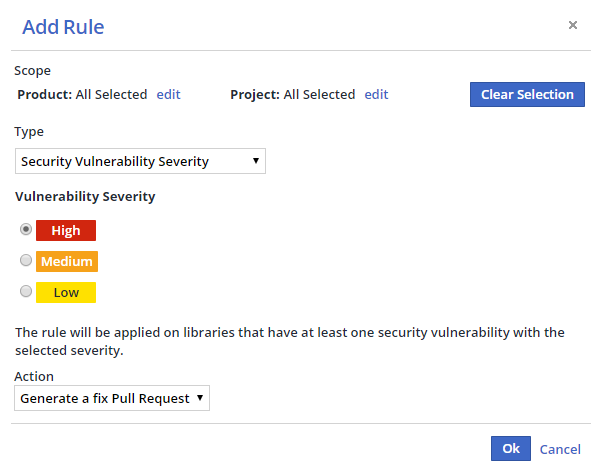
Click Add Rule. The Add Rule dialog box is displayed.
Select a Product and/or Project scope from the Scope area or leave at the default (applies to all of your WhiteSource Mend Products and Projects).
Select a rule type from the Type dropdown menu.
Click OK to create the rule.
Once you set up a Workflow Rule, WhiteSource Mend Remediate will start monitoring your selected repositories for vulnerable dependencies and generate corresponding fix Pull Requests.
Configuration of GitHub.com Credentials
| Info |
|---|
If you are running Remediate against github.com already, or making use of WhiteSource Mend for github.com, then you don’t need to provision credentials explicitly. |
...
For other use cases (including self-hosted GitHub Enterprise Server), to provide such credentials to the Remediate container, you should configure a github.com Personal Access Token into the environment variable GITHUB_COM_TOKEN. This token can belong to any github.com account and does needs only public read-only permissions. For details on creating such a token, click here.
WhiteSource Mend cannot provide customers with a token for accessing github.com as that would go against that platform’s Terms of Service.
Providing the Integration Activation Key
WhiteSource Mend Remediate can be configured to work with the integration activation key using either the prop.json configuration file or using environment variables.
NOTE: The environment variable takes precedence over an activation key value specified inside a prop.json file.
Providing the Integration Activation Key in prop.json
You can provide the integration's activation key to the Remediate container using a prop.json file.
Providing the Integration Activation Key using Environment Variables
You can provide the integration activation key by using the W4D_BOLT_OP_ACTIVATION_KEY environment variable inside the Remediate container.
Proxy Support
WhiteSource Mend Remediate can be configured to work with proxy servers using either the prop.json configuration file or using environment variables.
Proxy Configuration in prop.json
When configuring proxies using prop.json, the "no proxy" list will be automatically configured to match the VCS endpoint in use (i.e. the GitHub, GitLab or Bitbucket Server endpoint). Internally Remediate will convert these to HTTP_PROXY, HTTPS_PROXY and NO_PROXY environment variables and pass them to child processes such as npm and composer.
Proxy Configuration Using Environment Variables
WhiteSource Mend Remediate also supports the industry convention of HTTP_PROXY, HTTPS_PROXY and NO_PROXY. This provides more flexibility if you need to also configure any internal/private registries in the no proxy list so is the recommended configuration approach. Such variables will be passed transparently to child processes.
Automated Dependency Updates for Improved Dependency Health
Although remediating vulnerabilities should be the highest priority for dependency updating, it is recommended to adopt a proactive dependency update approach using Remediate’s “Renovate” capabilities.
WhiteSource’s Mend’s Renovate capabilities bring automated dependency updates to WhiteSource’s Mend’s repository integrations. By enabling Renovate, more than 50 package manager formats can be detected automatically and dependencies within updated, including numerous Infrastructure as Code managers such as Terraform and Ansible.
...
Vulnerability fixes are often discretely released days or weeks prior to public disclosure, and you may be lucky enough to frequently update using Renovate prior to disclosure and avoid a vulnerability notification altogether
Even if projects are not completely up-to-date, being reasonably up-to-date means that applying vulnerability remediations is much lower risk and therefore can be done more quickly, lowering the average time-to-resolution for CVEs
For highly nested dependencies, such as Containers and Infrastructure as Code where vulnerable components may be deeply transitive, staying up-to-date (e.g. with Docker base image updates) is one of the best ways to stay secure anyway
Integration with
...
Mend Renovate
WhiteSource Mend Renovate functionality can be enabled in WhiteSource Mend Remediate via an option in the .whitesource configuration file.
With Renovate functionality enabled, Remediate will then raise PRs/MRs not only for vulnerable dependencies but also for outdated dependencies too.
Renovate is designed for users who aim to keep their dependencies up-to-date, primarily for the reasons of:
...
Renovate itself is well-documented via its own documentation site. The Renovate docs are automatically generated based off the open source Renovate repository, so are unnecessary to duplicate here in full, however examples and clarifications will be provided below specifically for users of WhiteSource Mend Remediate.
Renovate Configuration
Renovate supports a range of different filenames, however for WhiteSource Mend Remediate integration only the .whitesource configuration file is used. Renovate is disabled by default so enabled by setting remediateSettings.enableRenovate = true like so:
...
Any configuration you place within the remediateSettings object will be used by Remediate similarly to how Renovate usually uses a renovate.json configuration file. Therefore, if you have an existing renovate.json file in a repository but are migrating to WhiteSource Mend Remediate then you'd copy paste its contents inside remediateSettings before removing the renovate.json file.
Recommended Starting Config
If you are new to Renovate, we recommend you start with the config:base preset config, which enables functionality such as maximum two dependency update PRs per hour as well as grouping well-known monorepo dependencies together:
| Code Block |
|---|
{
"remediateSettings": {
"enableRenovate": true,
"extends": ["config:base"]
}
} |
What Happens When Remediations Are Available
It's useful to understand how Remediate works if you have Renovate enabled with updates available while vulnerability fixes are also required at the same time. If a package dependency needs vulnerability remediation then Remediate reads the list of fixed versions and determines the minimum version that solves all known CVEs. It then uses a package rule to enforce that the remediation PR/MR for that package does not propose to update to the latest and instead updates to the lowest version that can resolve all open CVEs for the package. If an existing PR/MR exists proposing an update to the latest version but the minimum fix is lower, the existing PR/MR may be auto-closed by Remediate and replaced with the minimum fix PR/MR instead. This is intentional so that (a) teams can focus on the high priority remediation PR/MR, and (b) remediations cause the least changes possible so that they are simpler to verify and test.
Common Configuration Options and Examples
Renovate is highly configurable with many options, so here are the most commonly used ones to take a look at first:
...
If you have questions about any particular configuration option or are looking for examples of its use, you may find it useful to search existing Issues in Renovate's Config Help Repository on GitHub.
Merge Confidence
| Info |
|---|
For more information Merge Confidence, see here. |
...
To enable it for Renovate within WhiteSource Mend Remediate, add the following configuration within the remediateSettings section of your .whitesource file:
...
| Code Block | ||
|---|---|---|
| ||
{
"remediateSettings": {
"enableRenovate": true,
"prBodyDefinitions": {
"Age": "",
"Adoption": "",
"Passing": "",
"Confidence": ""
},
"packageRules": [
{
"datasources": [
"maven", "npm", "pypi"
],
"updateTypes": [
"patch",
"minor",
"major"
],
"prBodyColumns": [
"Package",
"Change",
"Age",
"Adoption",
"Passing",
"Confidence"
]
}
]
}
} |
Remediate Worker Horizontal Scalability
To scale Remediate to allow it to utilize additional containers, in order to process multiple repositories concurrently, you can enable Remediate Worker Horizontal Scalability. In this mode, the Remediate “worker” logic (which processes repositories) is separated from the Remediate “server” logic (scheduler, job queue and webhook handling) in a many-to-one relationship.
...